Salt Typhoon: Technical Analysis of the Pivot from Espionage to Infrastructure Capture
- Kedge Security Team

- Jan 3
- 4 min read
Updated: Feb 3
Executive Summary
For years, the industry has treated "Typhoon" actors (PRC-state-sponsored groups) as distinct silos: Volt for sabotage, Mustang for email theft. Salt Typhoon (also tracked as GhostEmperor, FamousSparrow, and UNC2286) has shattered those silos. By compromising the core backbone of U.S. broadband providers and specifically targeting Lawful Intercept (LI) systems, Salt Typhoon has achieved what few actors ever do: they didn't just breach the network; they captured the regulatory apparatus designed to police it. This technical analysis deconstructs the attack lifecycle, from edge exploitation to the exfiltration of wiretap data, to provide network architects with the technical clarity needed to defend against a threat that lives inside your router.
The Timeline: A Slow-Motion Crisis
While headlines broke in late 2024, the forensic reality is a campaign of "long dwell" persistence.
2020–2023 (Pre-Positioning): Early indicators of activity (tracked under the FamousSparrow moniker) showed probing of government entities and hotels worldwide. The group was refining its toolset, specifically the SparrowDoor backdoor and Demodex rootkit, focusing on low-noise persistence.
Early 2024 (The Surge): A strategic shift occurred. Telemetry confirms a massive uptick in scanning for vulnerabilities in Cisco, Fortinet, and Ivanti edge devices across North American ISPs, and impacting over 80 countries.
Late 2024 (The Discovery): Major U.S. broadband providers identified anomalous traffic flows. Investigations revealed that the compromise wasn't limited to corporate IT; the actors had pivoted into the Operational Technology (OT) management plane responsible for CALEA (Communications Assistance for Law Enforcement Act) compliance.
2025–Present: Post-breach analysis confirms that Salt Typhoon maintained undetected access for at least 18 months in some environments, utilizing the very infrastructure of the ISP to hide their traffic.

Technical Narrative: Anatomy of the Attack
The Salt Typhoon kill chain is defined by its reliance on network-centric Living off the Land (LotL). They do not smash windows; they pick locks using the admin’s own keys.
1. Entry Vectors: The "N-Day" Edge Rush
Salt Typhoon rarely burns zero-days. Instead, they weaponize N-day vulnerabilities—exploits for which a patch exists but has not yet been applied at scale.
Primary Vector: Exploitation of unpatched edge appliances.
Cisco IOS XE: Exploiting web UI vulnerabilities (similar to CVE-2023-20198) to bypass authentication.
Ivanti Connect Secure: Chaining authentication bypass and command injection flaws (CVE-2023-46805 / CVE-2024-21887).
Secondary Vector: Compromised credentials harvested from third-party contractors and managed service providers (MSPs) who have legitimate remote access to ISP infrastructure.

2. Lateral Movement: Ghosting the Router
Once they breach the edge, Salt Typhoon does not simply drop a binary and run. They inhabit the network device itself.
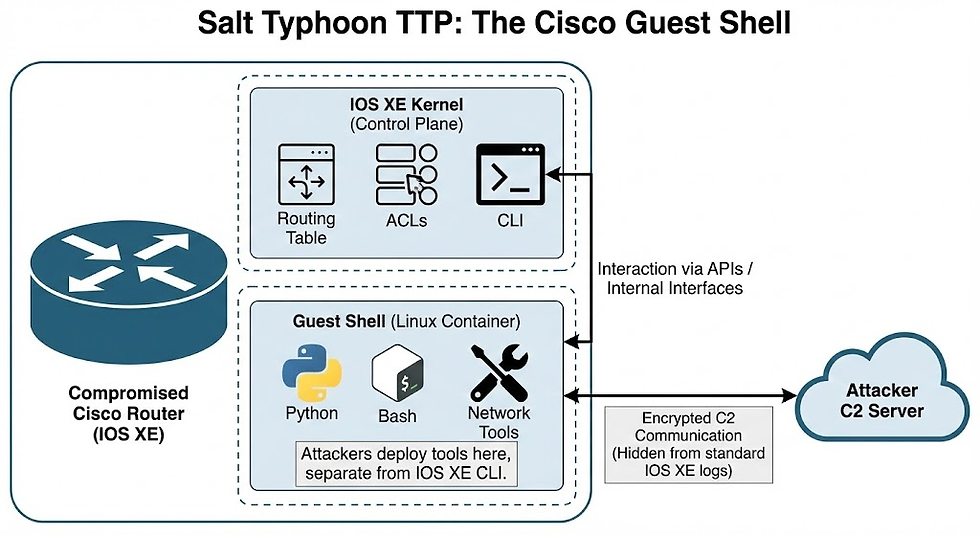
The "Guest Shell" Technique:
Modern Cisco routers run a Linux kernel. Salt Typhoon enables the Guest Shell—a virtualized Linux container designed for legitimate system administration (running Python scripts, etc.).
The TTP: They deploy their tools inside this container. Because the Guest Shell is distinct from the IOS XE command line, standard network auditing commands often fail to show the malicious processes running within the container.
SNMP Weaponization:
The attackers hunt for running-config files to extract SNMP Read/Write community strings.
Using these strings, they don't need malware to move laterally; they simply issue SNMP SET requests to reconfigure neighboring switches and routers, changing VLANs or opening interfaces without ever logging in via SSH.
3. The Objective: Compromising Lawful Intercept (CALEA)
This is the most critical aspect of the campaign. ISPs are legally required to maintain infrastructure for court-ordered wiretaps. These systems are highly sensitive and usually segmented.
The Pivot: Using the administrative access gained from the core routers, Salt Typhoon pivoted into the management VLANs hosting the Lawful Intercept (LI) mediation devices.
The Compromise: They did not need to break the encryption of the wiretaps. Instead, they accessed the Mediation Device—the server that aggregates the intercept data before it is handed off to law enforcement.
Data Stolen:
Call Data Records (CDR): Who is calling whom, when, and for how long.
Real-time Audio: In some confirmed instances, attackers could mirror the audio streams destined for law enforcement agencies.
Target Lists: Perhaps most damaging, they accessed the list of who the U.S. government is currently investigating.
4. Exfiltration: Hiding in the Tunnel
Traditional exfiltration (sending large zip files to a foreign IP) trips Data Loss Prevention (DLP) alerts. Salt Typhoon used the ISP's own routing protocols to smuggle data.

GRE Tunneling: The actors reconfigured compromised routers to establish Generic Routing Encapsulation (GRE) tunnels to attacker-controlled infrastructure.
Traffic Mirroring: They configured the router to mirror specific traffic of interest (e.g., traffic from the LI mediation device) into this GRE tunnel.
The Result: To the defensive stack, this looks like legitimate, encapsulated network routing traffic. The data flows out of the network at the packet layer, bypassing host-based proxies and firewalls entirely.
Mitigation: The Network-Centric Approach
Defending against an actor that has compromised the network control plane requires a pivot from endpoint security to network integrity.
Telemetry is King (NetFlow/IPFIX):
You cannot detect this with EDR agents, as you cannot install CrowdStrike on a Cisco router.
Action: Implement rigorous NetFlow analysis. Look for GRE tunnels with endpoints outside your trusted ASN. Alert on any traffic originating from the management interface of a router destined for the internet.
Verify the Integrity of the "Hardened" Edge:
Regularly audit the status of Guest Shells on network devices. If you don't use them, disable them globally.
Compare running configurations against a "known good" gold master (Golden Config) daily. Any deviation (e.g., a new ACL entry or SNMP string) triggers an immediate Sev-1 alert.
Segregate the Management Plane:
The management interfaces of your routers and switches should be in a VRF (Virtual Routing and Forwarding) instance that has zero route to the internet. Management traffic should strictly be internal.
Conclusion
Salt Typhoon has demonstrated that the "plumbing" of the internet is not just a transport layer; it is a battleground. By living off the land within routers and weaponizing lawful intercept systems, they have turned our own compliance infrastructure against us.
For the security practitioner, the mandate is clear: Trust nothing that you cannot verify—including the router that is passing your packets.

